
Version: 1.22016-04-22National Information Assurance Partnership

| Version | Date | Comment |
|---|---|---|
| v 1.2 | 2016-04-22 | Multiple clarifications based on NIAP TRRT inquiries Refactored FDP_DEC_EXT.1 into separate components |
| v 1.1 | 2014-11-05 | |
| v 1.0 | 2014-10-20 |
1. Introduction
1.1. Overview
1.2. Terms
1.2.1. Common Criteria Terms
1.2.2. Technology Terms
1.3. Compliant Targets of Evaluation
1.3.1. TOE Boundary
1.4. Use Cases
3. Security Problem Definition
3.1. Threats
3.2. Assumptions
3.3. Organizational Security Policies
4.1. Security Objectives for the TOE
4.2. Security Objectives for the Operational Environment
4.3. Security Objectives Rationale
5.1. Security Functional Requirements
5.1.1. Cryptographic Support (FCS)
5.1.2. User Data Protection (FDP)
5.1.3. Security Management (FMT)
5.1.4. Privacy
5.1.5. Protection of the TSF (FPT)
5.1.6. Trusted Path/Channel (FTP)
5.2. Security Assurance Requirements
5.2.1. Class ASE: Security Target
5.2.2. Class ADV: Development
5.2.3. Class AGD: Guidance Documentation
5.2.4. Class ALC: Life-cycle Support
5.2.5. Class ATE: Tests
5.2.6. Class AVA: Vulnerability Assessment
Appendix A: Optional Requirements
Appendix B: Selection-Based Requirements
Appendix C: Objective Requirements
Appendix D: Entropy Documentation and Assessment
Appendix E: References
Appendix F: Acronyms
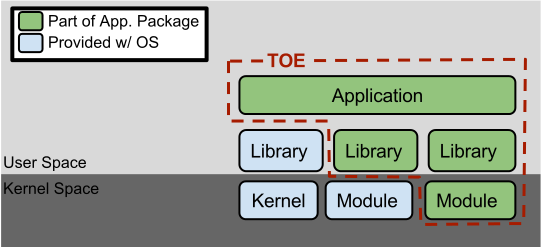 Figure 1: TOE as an Application and Kernel Module Running on an Operating System
Figure 1: TOE as an Application and Kernel Module Running on an Operating System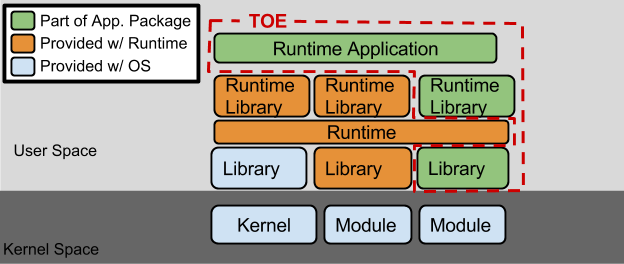 Figure 2: TOE as an Application Running in an Execution Environment Plus Native Code
Figure 2: TOE as an Application Running in an Execution Environment Plus Native Code| Threat, Assumption, or OSP | Security Objectives | Rationale |
| T.NETWORK_ATTACK | O.PROTECTED_COMMS, O.INTEGRITY, O.MANAGEMENT | |
| T.NETWORK_EAVESDROP | O.PROTECTED_COMMS, O.QUALITY, O.MANAGEMENT | |
| T.LOCAL_ATTACK | O.QUALITY | |
| T.PHYSICAL_ACCESS | O.PROTECTED_STORAGE | |
| A.PLATFORM | OE.PLATFORM | |
| A.PROPER_USER | OE.PROPER_USER | |
| A.PROPER_ADMIN | OE.PROPER_ADMIN |
use no DRBG functionality,
invoke platform-provided DRBG functionality,
implement DRBG functionality
] for its cryptographic operations.javax.crypto.KeyGenerator
class or the java.security.SecureRandom class or /dev/random
or /dev/urandom.
SecRandomCopyBytes or uses /dev/random directly to acquire random.
/dev/random
or /dev/urandom.
/dev/random.
/dev/random to
acquire random.
not store any credentials,
invoke the functionality provided by the platform to securely store [assignment: list of credentials] ,
implement functionality to securely store [assignment: list of credentials]
] to non-volatile memory.KeyStore or the Android KeyChain to store certificates.
Keychain.
keyrings.
Key Management Framework (KMF).
Keychain.no hardware resources,
network connectivity,
camera,
microphone,
location services,
NFC,
USB,
Bluetooth,
[assignment: list of additional hardware resources]
] .App permissions > Settings > Security and Privacy > Application
Permissions > Select application in question, it will list which platform resource
are approved/denied and can be changed.
no sensitive information repositories,
address book,
calendar,
call lists,
system logs,
[assignment: list of additional sensitive information repositories]
] .no network communication,
user-initiated communication for [assignment: list of functions for which the user can initiate network communication] ,
respond to [assignment: list of remotely initiated communication ] ,
[assignment: list of application-initiated network communication]
] .leverage platform-provided functionality to encrypt sensitive data,
implement functionality to encrypt sensitive data,
not store any sensitive data
] in non-volatile memory.MODE_PRIVATE flag set.
SharedPreferences and/or PreferenceActivity classes
for storing configuration data, where package is the Java package
of the application.
user defaults system or key-value store for storing all
settings.NSUserDefaults class.
ls -alR|grep -E '^.......(r|-w|--x)' inside the application's
data directories to ensure that all files are not world-accessible
(either read, write, or execute).
The command should not print any files.
The evaluator shall also verify that no sensitive data is written to
external storage which could be read/modified by any other application.
ls -alR|grep -E '^.......(r|-w|--x)' inside the application's
data directories to ensure that all files are not world-accessible
(either read, write, or execute).
The command should not print any files.
The evaluator shall also verify that no sensitive data is written to
external storage as this data can be read/modified by any application containing the
READ_EXTERNAL_STORAGE and/or WRITE_EXTERNAL_STORAGE permissions.find . -perm /007
inside the application's data directories to ensure that all files are
not world-accessible (either read, write, or execute).
The command should not print any files.
find . \( -perm -001 -o -perm -002 -o -perm -004 \)
inside the application's data directories to ensure that all files are not
world-accessible (either read, write, or execute).
The command should not print any files.
find . -perm +007 inside
the application's data directories to ensure that all files are not world-accessible
(either read, write, or execute).
The command should not print any files.
no management functions,
enable/disable the transmission of any information describing the system's hardware, software, or configuration ,
enable/disable the transmission of any PII ,
enable/disable transmission of any application state (e.g. crashdump) information,
enable/disable network backup functionality to [assignment: list of enterprise or commercial cloud backup systems] ,
[assignment: list of other management functions to be provided by the TSF]
] .not transmit PII over a network ,
require user approval before executing [assignment: list of functions that transmit PII over a network ]
] .pmap -x PID
to ensure the two different instances share no mapping locations.
pmap -x PID
to ensure the two different instances share no mapping locations.
vmmap PID
to ensure the two different instances share no mapping locations.
not allocate any memory region with both write and execute permissions ,
allocate memory regions with write and execute permissions for only [assignment: list of functions performing just-in-time compilation]
] ./NXCOMPAT flag was used during
compilation to verify that DEP protections are enabled for the application.
-fstack-protector-strong or -fstack-protector-all
flags are used.
The -fstack-protector-all flag is preferred but
-fstack-protector-strong is acceptable.
-fstack-protector-strong or -fstack-protector-all flags
are used. The -fstack-protector-all flag is preferred but
-fstack-protector-strong is acceptable. /GS flag was used during compilation. The evaluator shall run a tool,
like BinScope, that can verify the correct usage of /GS
-fstack-protector-strong or
-fstack-protector-all flags are used. The
-fstack-protector-all flag is preferred but
-fstack-protector-strong is acceptable.
If the application is built using any other compiler, then the evaluator shall determine that
appropriate stack-protection has been used during the build process.
-fstack-protector-strong or
-fstack-protector-all flags are used. The
-fstack-protector-all flag is preferred but
-fstack-protector-strong is acceptable. If the application is built
using clang, it must be compiled and linked with the
-fsanitize=address flag.
If the application is built using any other compiler, then the evaluator shall determine that appropriate stack-protection has been used during the build process.
-fstack-protector-strong or
-fstack-protector-all flags are used. The
-fstack-protector-all flag is preferred but
-fstack-protector-strong is acceptable. If the application is built
using clang, it must be compiled and linked with the
-fsanitize=address flag.
If the application is built using any other compiler, then the evaluator shall determine that appropriate stack-protection has been used during the build process.
-fstack-protector-strong or
-fstack-protector-all flags are used. The
-fstack-protector-all flag is preferred but
-fstack-protector-strong is acceptable.
If the application is built using any other compiler, then the evaluator shall determine that
appropriate stack-protection has been used during the build process.
deb format. not transmit any data,
not transmit any sensitive data,
encrypt all transmitted sensitive data with [selection, at least one of: HTTPS, TLS, DTLS, SSH as conforming to the Extended Package for Secure Shell] ,
encrypt all transmitted data with [selection, at least one of: HTTPS, TLS, DTLS, SSH]
] between itself and another trusted IT product.If TLS is selected, then evaluation of elements from FCS_TLSC_EXT.1 is required.
If HTTPS is selected, then evaluation of elements from FCS_HTTPS_EXT.1 is required.
If DTLS is selected, then evaluation of elements from FCS_DTLS_EXT.1 is required.
If SSH is selected, the TSF shall be validated against the Extended Package for Secure Shell.
128 bit,
256 bit
] .a software-based noise source,
no other noise source
] with a minimum of [selection:128 bits,
256 bits
] of entropy at least equal to the greatest security strength (according to NIST SP 800-57) of the keys and hashes that it will generate.generate no asymmetric cryptographic keys,
invoke platform-provided functionality for asymmetric key generation,
implement asymmetric key generation
] .[RSA schemes] using cryptographic key sizes of [2048-bit or greater] that meet the following: [selection:
FIPS PUB 186-4, “Digital Signature Standard (DSS)”, Appendix B.3 ,
ANSI X9.31-1998, Section 4.1
] ,[ECC schemes] using [“NIST curves” P-256, P-384 and [selection: P-521 , no other curves ] ] that meet the following: [FIPS PUB 186-4, “Digital Signature Standard (DSS)”, Appendix B.4] ,
[FFC schemes] using cryptographic key sizes of [2048-bit or greater] that meet the following: [FIPS PUB 186-4, “Digital Signature Standard (DSS)”, Appendix B.1]
] .[Elliptic curve-based key establishment schemes] that meets the following: [NIST Special Publication 800-56A, “Recommendation for Pair-Wise Key Establishment Schemes Using Discrete Logarithm Cryptography”] ,
[Finite field-based key establishment schemes] that meets the following: [NIST Special Publication 800-56A, “Recommendation for Pair-Wise Key Establishment Schemes Using Discrete Logarithm Cryptography”] ,
No other schemes
] .AES-GCM (as defined in NIST SP 800-38D),
no other modes
] and cryptographic key sizes 256-bit and [selection: 128-bit, no other key sizes] .
# Input: PT, IV, Key
for i = 1 to 1000:
if i == 1:
CT[1] = AES-CBC-Encrypt(Key, IV, PT)
PT = IV
else:
CT[i] = AES-CBC-Encrypt(Key, PT)
PT = CT[i-1]
The ciphertext computed in the 1000th iteration (i.e.,
CT[1000]) is the result for that trial. This result shall be
compared to the result of running 1000 iterations with the same
values using a known good implementation.
SHA-1,
SHA-256,
SHA-384,
SHA-512,
no other algorithms
] and message digest sizes [selection:160,
256,
384,
512,
no other message digest sizes
] bits that meet the following: FIPS Pub 180-4.RSA schemes using cryptographic key sizes of 2048-bit or greater that meet the following: FIPS PUB 186-4, “Digital Signature Standard (DSS)”, Section 4 ,
ECDSA schemes using “NIST curves” P-256, P-384 and [selection: P-521, no other curves] that meet the following: FIPS PUB 186-4, “Digital Signature Standard (DSS)”, Section 5
] .SHA-1,
SHA-384,
SHA-512,
no other algorithms
] with key sizes [assignment: key size (in bits) used in HMAC] and message digest sizes 256 and [selection: 160, 384, 512, no other size] bits that meet the following: FIPS Pub 198-1 The Keyed-Hash Message Authentication Code and FIPS Pub 180-4 Secure Hash Standard.TLS_DHE_RSA_WITH_AES_128_CBC_SHA256 as defined in RFC 5246,
TLS_DHE_RSA_WITH_AES_256_CBC_SHA256 as defined in RFC 5246,
TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256 as defined in RFC 5289,
TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256 as defined in RFC 5289,
TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384 as defined in RFC 5289,
TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384 as defined in RFC 5289,
TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256 as defined in RFC 5289,
TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256 as defined in RFC 5289,
TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 as defined in RFC 5289,
TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 as defined in RFC 5289,
TLS_RSA_WITH_AES_128_CBC_SHA256 as defined in RFC 5246,
TLS_RSA_WITH_AES_256_CBC_SHA256 as defined in RFC 5246,
no other cipher suite
] .TLS_DHE_RSA_WITH_AES_128_CBC_SHA256 as defined in RFC 5246,
TLS_DHE_RSA_WITH_AES_256_CBC_SHA256 as defined in RFC 5246,
TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256 as defined in RFC 5289,
TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256 as defined in RFC 5289,
TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384 as defined in RFC 5289,
TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384 as defined in RFC 5289,
TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256 as defined in RFC 5289,
TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256 as defined in RFC 5289,
TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 as defined in RFC 5289,
TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 as defined in RFC 5289,
TLS_RSA_WITH_AES_128_CBC_SHA256 as defined in RFC 5246,
TLS_RSA_WITH_AES_256_CBC_SHA256 as defined in RFC 5246,
no other cipher suite
] .| Identifier | Title |
|---|---|
| [CC] |
|
| [CEM] | |
| [CESG] | |
| [CSA] | |
| [OMB] |
| Acronym | Meaning |
|---|---|